Wallet
A Bitcoin wallet is a file that contains a collection of private keys.
Contents
Bitcoin Qt
The original Bitcoin client wallet file is named wallet.dat and contains[1]:
- keypairs for each of your addresses
- transactions done from/to your addresses
- user preferences
- default key
- reserve keys
- accounts
- a version number
- Key pool
- Since 0.3.21: information about the current best chain, to be able to rescan automatically when restoring from a backup.
The data file for the wallet is wallet.dat and is located in the Bitcoin data directory.
It is intended that a wallet be used on only one installation of Bitcoin at a time. Attempting to clone a wallet for use on multiple computers will result in "weird behavior"[2].
The format of this file is Berkeley DB. Tools that can manipulate wallet files include pywallet.
Armory
The Armory client uses a custom binary wallet format.
Blockchain.info
Blockchain.info use a plain text JSON wallet format documented here. Private keys Keys are stored in base58.
Coinkite
![]() Coinkite is the only web wallet using "HD Wallet (BIP32)" technology, which can be shared partially or entirely with different systems, each with or without the ability to spend coins here. Private keys Keys are sent to you encrypted with AES-256-CBC.
Coinkite is the only web wallet using "HD Wallet (BIP32)" technology, which can be shared partially or entirely with different systems, each with or without the ability to spend coins here. Private keys Keys are sent to you encrypted with AES-256-CBC.
HolyTransaction
HolyTransaction is your universal multi-currency wallet with instant exchange. You can send payments in one digital currency, and receive in another. It's designed for nontechnical users. Mobile wallet client available on any device with HTML5 support.
Multibit
Multibit uses the bitcoinj protobuf wallet file.
Coinprism
![]() Coinprism is the first colored coin web wallet. Coinprism is similar to other web wallets, except you can store, issue, send and receive colored coins and not only normal Bitcoins. Note that the site is currently in invite-only beta.
Coinprism is the first colored coin web wallet. Coinprism is similar to other web wallets, except you can store, issue, send and receive colored coins and not only normal Bitcoins. Note that the site is currently in invite-only beta.
Bitcoin Wallet
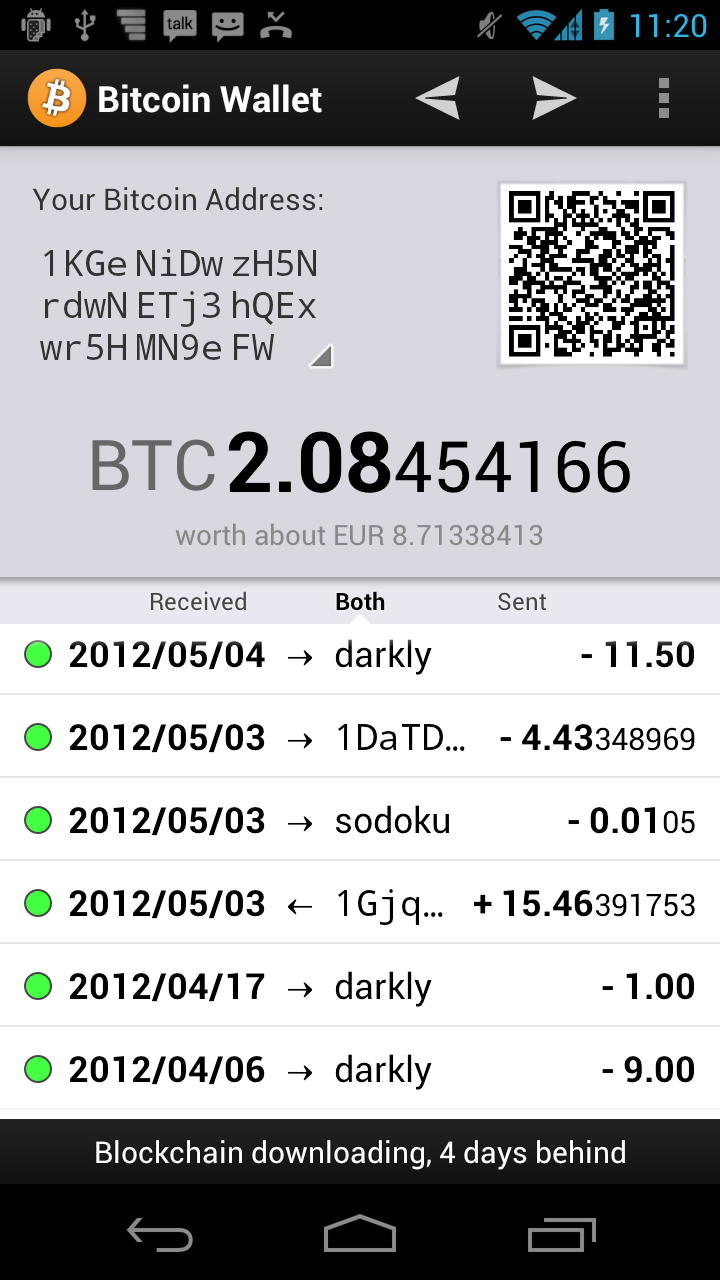 Bitcoin Wallet uses the bitcoinj protobuf format for its wallet file. However, due to Android isolation of applications, it is impossible to access the wallet file as a non-root user.
Bitcoin Wallet uses the bitcoinj protobuf format for its wallet file. However, due to Android isolation of applications, it is impossible to access the wallet file as a non-root user.
Email Tip Bot
Email Tip Bot is a wallet that works entirely through email. This makes it the only native solution to sending bitcoins on iOS devices, like the iPhone and iPad. It is secure against email spoofing, but can be compromised by anyone who has read access to your email.